• Target motion reports as ASTERIX CAT-48
• Primary and ADS-B targets fused before evaluation
• Database of assets and associated priority
• Database of weapon types and availability
• Flexible and configurable threat scoring
• Threat classification by user
• Threat score based on target range, speed, automatic/user classification, origin, course deviation, manoeuvrability and asset priority
• Fully integrated with ASD-100 for simultaneous display of multiple threats and per-threat engagement for first-stage weapon assignment
• Weapon assignment based on threat dynamics and weapon capability and location
• Fully distributed architecture supports multiple operator displays and target engagement
TEWA
Threat Evaluation & Weapon Assignment
For cost-effective air defence systems, supporting modern and legacy radars.
Contact Sales

Automatically Detects & Scores Threats
Calculates a threat score from user-assigned threat levels, automated classification, track speed, origin and manoeuvrability.
Ask a QuestionKey Features
Used as the basis for a highly capable and cost-effective integrated air defence system
Wide Support for Radars
The software can integrate with multiple legacy analogue radars as well as the latest primary and IFF radars, providing an affordable solution that avoids the cost of replacing radars.
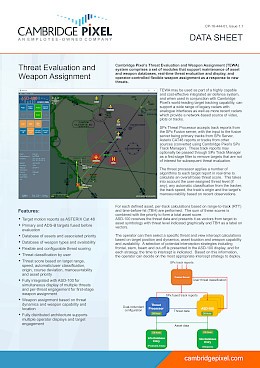
Track reports can be provided from the SPx Fusion Server, with the input to the fusion server being primary tracks from SPx Server and/or ADS-B position reports. These track reports may optionally be passed through SPx Track Manager as a first-stage filter to remove targets that are not of interest for subsequent threat evaluation.
Threat Processor
The threat processor applies a number of algorithms to each target report in real-time to calculate an overall base threat score. This takes into account the user-assigned threat level (if any), any automatic classification from the tracker, the track speed, the track’s origin and the target’s manoeuvrability based on recent observations.
For each defined asset, per-track calculations based on range-to-track (RTT) and time-before-hit (TBH) are performed. The sum of these scores is combined with the priority to form a total asset score.
Radar Display with Weapon Assignment
ASD-100 receives the threat data and presents it as vectors from target to asset symbology with threat level indicated graphically and TBH as a label on vectors.
The operator can then engage with a specific threat and view intercept calculations based on target position and dynamics, asset location and weapon availability. A selection of potential interception strategies including frontal, stern, beam and cut-off is presented in the ASD-100 display, and for each strategy, the time to intercept is indicated. Based on this information, the operator can decide on the most appropriate intercept strategy to deploy.
Asset & Weapon Database
Assets and weapons are held in a custom distributed database implemented using Cambridge Pixel’s Network Data Sharing capability. Any changes to objects in the database are immediately reflected to all other database entry instances and consumers of the data including ASD-100 and the threat processor. This provides a highly resilient architecture that is not dependent on the continued operation of specific nodes.

TEWA Details
Real-World Application
Cambridge Pixel have experience in providing and installing TEWA as part of a national air defence system to monitor country-wide threats using existing radar infrastructure.